
Background Overview
On August 3, 2022, a large-scale attack occurred on the Solana blockchain, and a large number of users’ SOL and SPL tokens were transferred without their knowledge. The Slope wallet team invites the SlowMist security team to analyze and follow up. During our initial investigation our analysis showed that the Slope wallet version released on 06/24/2022 later version sent private key or mnemonic phrases to Sentry’s service.
However, from the investigation of the Slope wallet application to the present, it is impossible to clearly prove that the root cause of the incident lies with the Slope wallet, so the SlowMist security team began to analyze and collect evidence on the Slope server.
Analysis Overview
After the incident, the attention of all parties mainly focused on investigating the root cause of the incident and the possibility of tracking and recovering the stolen funds. So the SlowMist security team made relevant plans to investigate by analyzing off-chain and on-chain activities.
We concentrated on determining the underlying cause of the incident on the Slope server. There is a significant amount of technical work to be completed, and further evidence is required to explain the fundamental cause of this incident.
The SlowMist security team relies primarily on MistTrack’s monitoring and analysis capabilities, data tagging capabilities, and intelligence capabilities to identify and track the on-chain activities of the hackers. Additionally, we are collaborating with the Slope team on the prospect of recovery. By offering bug bounties, the Slope team is also attempting to engage with hackers in an effort to encourage them to return the stolen assets. They strive to promote the healthy growth of Solana’s ecosystem.
This article will only share staged investigations with community members. There is still a significant amount of ongoing and evolving analysis work. SlowMist, as well as other third-party security teams are all working diligently to help with the investigation. We trust that this situation will ultimately be resolved.
Note: The Sentry service involved in this article refers to the Sentry service deployed privately by the Slope team, not the interface and service officially provided by Sentry.
Before we complete the analysis, let’s go over some of the issues raised throughout the analytical process in the previous article:
Q1. Is it a common security issue for Sentry’s service to collect users’ wallet mnemonics?
A: Sentry is primarily used to collect abnormal or error log information from running application services.In the event of an invalid configuration, unexpected data, such as a private key or mnemonic, and other information, can be collected. As a result, it is not a common security concern. Developers should remember not to enable debug mode in the build environment when using the third party application monitoring service.
Q2. Phantom employs Sentry; will the Phantom wallet be affected as a result?
A: Despite the fact that Phantom makes use of the third party application monitoring service, SlowMist has not detected Sentry’s behavior of uploading private keys/mnemonics by monitoring previous versions of the Phantom wallet.
Q3. What accounts for the remaining 60% of compromised users?
A: After comparing the addresses produced from the server’s private key and mnemonic (including the HD address) with the victim’s address, it was discovered that they overlap with 5 ETH addresses and 1388 Solana addresses. In accordance with the ongoing investigation, there is no conclusive evidence to explain why other users’ wallets were compromised.
Q4. Was the official Sentry server hacked, given the popularity of the service? What prompted the deliberate attack of the cryptocurrency ecosystem?
A: There is currently no evidence that the official Sentry server has been infiltrated or compromised. Slope deployed Sentry on-premise, no cloud infrastructure provided by Sentry itself was involved or compromised.
Off-Chain Analysis
SlowMist is primarily concerned with examining whether off-chain servers and associated backend services may be compromised, such as investigating the risk of perimeter server assets of the Slope server, the intrusion traces of the server, and analyze the possibility of Sentry (PostgreSQL) database, server snapshot, and DNS hijacking.
1. Risk evaluation of peripheral server infrastructure
When the Slope team discovered that the mnemonic and private key information supplied by the Slope wallet was compromised, they shunt down the services 15 mins after the incident was revealed. As a result, the Slope wallet’s services became no longer accessible. We gathered data about Slope’s peripheral server infrastructure, such as subdomains and IP addresses under the slope.finance domain name, in order to perform a simulated penetration test analysis and diagnostic. Analysis and penetration testing have not revealed any vulnerability points that can be immediately penetrated from the presumed peripheral entry points.
2. Server intrusion trace analysis
It primarily investigates the Sentry server’s internal activities, such as server login logs, system historical operation commands, suspicious processes, suspicious network connections, suspicious system scheduled tasks, data deletion and acquisition operations, and so on. The same intrusion is also carried out by 5 Docker services on the server. The investigation revealed several suspicious login IPs: 113.*.*.*, 114.*.*.*, 153.*.*.*, these IPs accessed the backend of the third party application monitoring service before June 24. Although this happened before the time when the private key and mnemonic were collected (June 24), since these login requests took place before the start of the vulnerability and were not observed after, we do not think they are linked to the exploit. Nevertheless, further investigation on these is in progress.
3. PostgreSQL Database analysis
Because the mnemonic and private key are sent back to the server by the Slope wallet’s third party application monitoring service, we also investigated areas in the server where the private keys or mnemonics potentially reside. We later determined that this was the case. The private keys or mnemonics were most likely to be found in the following locations:
- In Sentry’s database table
- In the database log of PostgreSQL
- In the deleted data of the snapshot disk
- In the Docker runtime data file
During the investigation, it was discovered that the third party application monitoring service utilized the PostgreSQL database, where third party application monitoring service’s private key and mnemonic data could be found in the data field of the nodestore_node table.
The following details were discovered:
- From 07/28 to 08/05, the private key and mnemonic data contents were stored in the nodestore_node table.
- After decrypting and examining the data, we discovered that the data uploaded on June 29, 2022 was the earliest data recorded in the private key or mnemonic database, implying that the data collected by Sentry on June 29 was delayed by one month.It was stored in the PostgreSQL database’s nodestore_node table since 07/28. However, this is just a minor portion of the delayed data, since the majority of the private key and mnemonic collecting period was focused between 07/28 to 08/05.
- Further investigation of the database operation log found that there was a record of SQL statement execution failure in the nodestore_node table before 07/28 due to a key-value conflict. After in-depth investigation and communication, it was found that it was due to a Kafka service error that caused no data to be written.
- Some data must be restored again since it could not be restored to the whole data set during log recording and data recovery. As a result, the data that can be fully recovered was decrypted first. There were 189 ETH addresses, 4,914 Solana addresses and 5,073 mnemonics that have been decrypted. However, there are 42 ETH addresses and 9,231 Solana addresses associated with this incident. After comparing the addresses (including HD addresses) derived from the private key and mnemonic on the server, it was found that there were 5 ETH addresses and 1,388 Solana addresses that intersected with the victim. (This doesn’t include the small quantity of data that needed to be restored prior to decryption)
- Another internal test application, com.slope.game, contained private key and mnemonic report data in March, according to the database operation log. The internal test application was not released to the general public.
4. Server Snapshot Analysis
SlowMist examined Sentry’s cloud server snapshot, recovered deleted data from the server disk, and discovered private key and mnemonic information in the data that was recovered.
5. Analysis of the possibility of DNS hijacking
Through the capabilities of all parties and global intelligence resources, including the query and analysis of DNS resolution data, SlowMist presently lacks definitive proof that the domain name o7e.slope.finance has ever been the subject of a DNS hijacking event.
Conclusions of Off-chain Investigation and Analysis:
According to the current investigation we can draw the following conclusions:
* Peripheral server infrastructure: no vulnerable points of direct intrusion into peripheral servers have been discovered, no trace of server intrusion was found.
* Server intrusion trace analysis: no trace of server intrusion was found.However, the suspicious IP (113.*.*.*,114.*.*.*,153.*.*.*) still needs to be investigated. The private key and mnemonic information has been found in database tables, database log files, and recovered data from deleted files.
* Client-server communication: no evidence of DNS hijacking has been found for now.
On-chain Analysis
The on-chain segment focuses primarily on evaluating susceptible funds, moving stolen assets, and investigating hacker traces, with a particular emphasis on the following points:
1. Risk Capital Assessment
SlowMist allocated vulnerable assets into two categories based on stolen funds from the Solana, ETH, and BSC network.
Risk capital: Funds for which the hacker has access to an address.
Suspected risk capital: Funds that hackers may have access to.
Risk capital assessment based on the following list of addresses (mainly Solana & ETH network):
- Mnemonic of stolen addresses connected to the addresses on another network
- Mnemonic of the stolen address derived from the derived path
Exclude the list of risk capital addresses, and evaluate suspected risk capital based on the following address lists (mainly Solana & ETH network):
- The address where the mnemonic/private key record exists on the Slope server
- Mnemonics that exist on the Slope server connected to the addresses of other networks
- The address derived from the derived path of the mnemonic that exists on the Slope server
No large transferable risk funds and potentially risky funds were identified.
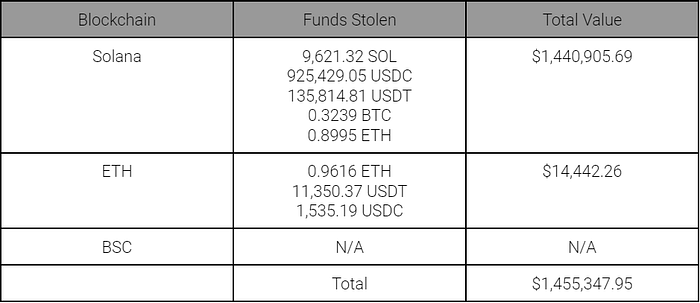
2. Statistics of Stolen Funds
To avoid the impact of stolen junk currencies, we decided to only included funds that were stolen of major coins:
Solana network: SOL, USDC, USDT, BTC and ETH.
ETH network: ETH, USDT, USDC and PAXG.
The value of the stolen coins is the price on the day of the theft (00:00 AM UTC on August 3rd).
1 SOL = $38.54
1 BTC = $22,846.51
1 ETH = $1,618.87
1 PAXG = $1,759.64
1 BNB = $298.36

On the Slope server, we examined the addresses (including HD addresses) produced from the encrypted private key and mnemonic, as well as the victim’s addresses on the blockchain. There are 5 ETH addresses and 1,388 Solana addresses that are associated with the victim. The statistics of the stolen funds for these interconnected addresses are as follows. This accounts for 31.42% of the total stolen funds:
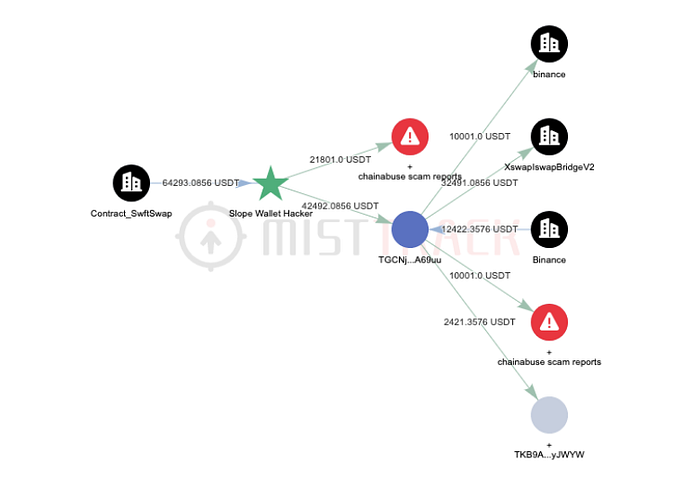
3. Money Transfer Analysis
Solana Network:
Funds were not transferred any further by the time of this publication.
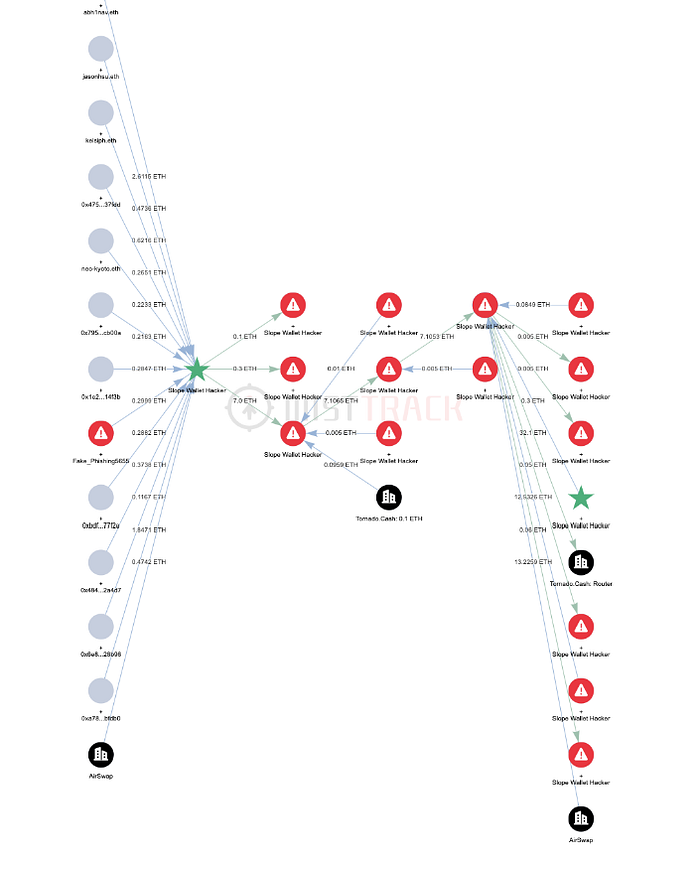
ETH Network:
- 21,801 USDT was transferred to a personal wallet (we suspected it to be an OTC exchange address based on on-chain analytics and MistTrack’s Address Label Database). We’re currently working with all parties to trace the identity of the hacker.
- Most of the remaining funds were converted to ETH and transferred to Tornado.Cash.
BSC Network:
Funds were not transferred any further by the time of this publication.
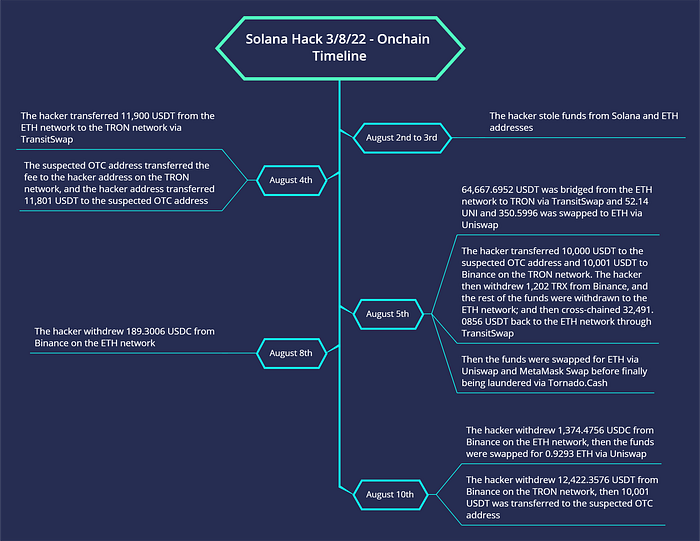
4. Event Timeline Analysis
The timeline is as follows, based on the behavior of the hacker’s activity:
5. Hacker Trace Analysis

Initial Transfer:
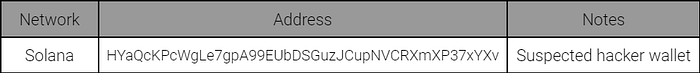
The initial incoming transactions on the hacker’s wallets 1, 2, 3, and 4 were 0.1 sol, which was transferred from the suspected hacker wallet on the Solana network. After analyzing the trace activity on the blockchain, we suspect that the suspected hacker wallet may be the hacker’s address. However, it’s more likely that it’s a victim’s address instead.
Hackers’ tools used for laundering funds:
- TransitSwap
- Uniswap
- MetaMask Swap
Hackers’ method used for laundering funds:
- Transfer to a suspected OTC personal wallet address (mentioned above)
- Transfer to Tornado.Cash
Hackers’ addresses associated with exchanges/platforms:
Direct Connections:
- On the TRON network, hackers deposit USDT to Binance on August 5th.
Deposit address: TE4bkS2PYqWxijgh5eqEz9A5jLn7HcS6fn,
Deposit Transaction Hash: b6615bf10b2e619edc9315a08f89732664adc9d385c980f77caa6e82872fe376
- On the TRON network, hackers withdrew TRX from Binance on August 5.
Withdrawal Transaction Hash:
0e012643a7db1b8c5d1f27447b16e313d4b3f89efaa22b3661188fe399cd2d0e
- On the ETH network, hackers withdrew ETH from Binance on August 5.
Withdrawal Transaction Hash:
0xd035e009173e968d8f72de783f02655009d6f85ef906121e5b99b496a10283dd
- On the ETH network, hackers withdraw USDC from Binance on August 8.
Withdrawal Transaction Hash:
0xff60f24f8ebd874a1e5da8eae44583af554af9a109a9bd7420da048f12c83cdc
- On the ETH network, hackers withdraw USDC from Binance on August 10.
Withdrawal Transaction Hash:
0xc861c40c0e53f7e28a6f78ec9584bfb7722cec51843ddf714b9c10fc0f311806
- On the TRON network, hackers withdrew USDT from Binance on August 10.
Withdrawal Transaction Hash:
10c4186e4d95fb2e4a1a31a18f750a39c0f803d7f5768108d6f219d3c2a02d26
Indirect Connection:
- The suspected wallet of the hacker on the Solana network withdrew SOL from Binance on January 8.
Withdrawal Transaction Hash:
668jpJec7hiiuzGDzj4VQKSsMWpSnbzt7BLMGWQmrGvHVQQbNGc3i1g8dCj2F5EAxFT8oDG5xWPAeQUMEMBTjhZs
- The suspected wallet of the hacker on the Solana network has on-chain traces of interaction with the Solrazr IDO program.
Transaction Hash: 2LxLhL7oAiTyHGrAXCZEJyazQQLM7veaKvqUZL6iPkonL4wPLHcwV66MFX3ERyWvJtdd2wFdKfgKUuT1oAv2XepK
- The suspected OTC personal wallet address (mentioned above) has deposits and withdrawals associated with Binance, Kucoin, and OKX exchanges.

Correlation of Suspected OTC Personal Wallet Addresses
The suspected OTC personal wallet address (TGBrAiVArhs5Cqp2CGMYUpSmkseznv1Ng7) is linked to money laundering activities spread across different instances, including phone scams, USDT and TRC20 theft.
On-chain Analysis (Attachments)
Special thanks to @greysign1.
