
Background
On January 27, 2021, according to the SlowMist Zone intelligence, SushiSwap was attacked again. The problem was that the transaction fee of the DIGG-WBTC trading pair was taken away by the attacker through special means. The SlowMist security team immediately intervened in the analysis of related incidents after receiving the intelligence. The following are the details of the attack.
What is SushiMaker
SushiMaker is an important component of the SushiSwap protocol. It is used to collect the handling fee of each trading pair of SushiSwap, and by setting the routing of each token, the handling fee of different trading pairs is finally converted into sushi tokens, which will give back Holder of sushi token. This process happens on the SushiMaker contract.
What is constant product
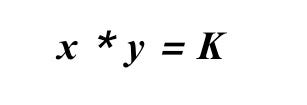
The formula for constant product is very simple. Without calculating the commission, the formula for constant product is
In other words, each exchange actually follows this formula, and the K value remains unchanged before and after the transaction. During the exchange process, since the K value remains unchanged, the formula will look like this
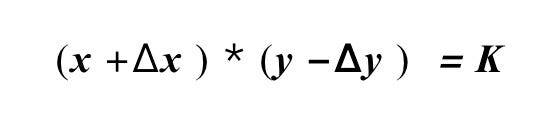
Where X represents the token to be sold and Y represents the token to be purchased, so the number of tokens that can be exchanged each time will look like this
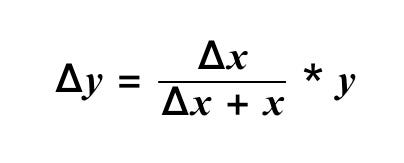
It can be seen from the formula that the upper limit of the exchange amount of output token Y depends on the number of Y tokens, and has nothing to do with the number of X tokens. On the other hand, if the number of X tokens to be sold is large, But the number of Y tokens is very small, so a large number of X tokens can only be exchanged for a small amount of Y tokens, and this exchange price will deviate a lot from the normal transaction price. This is the so-called slippage. The key to this attack.
Attack analysis
On November 30, 2020, SushiSwap had an attack because of the SushiMaker problem. This attack is similar to the first attack, but there are differences in the process. Compared with the old contract, in the new contract, the handling fee will be used to find specific exchange routes for the tokens in different trading pairs during the exchange process through the bridgeFor function, and then exchange.
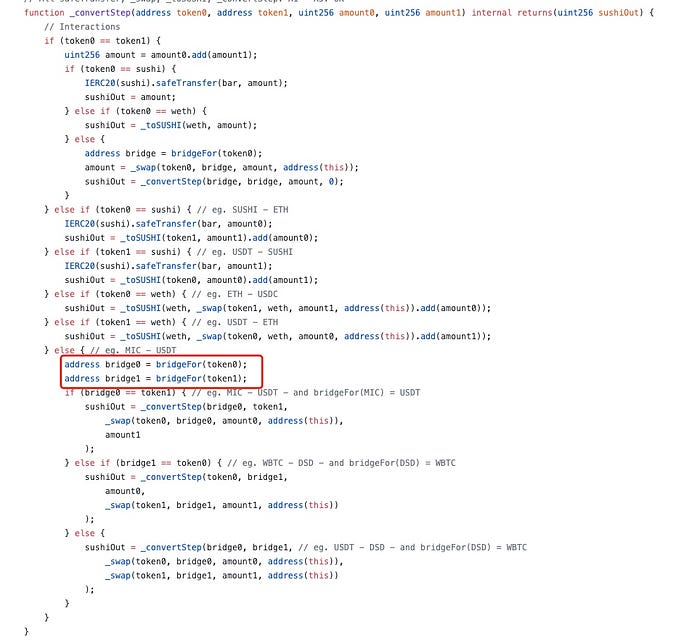
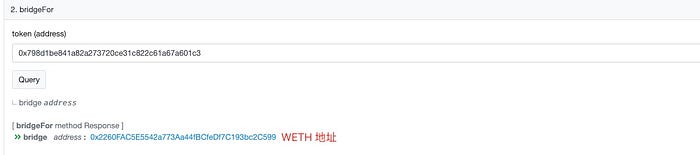
The logic of the bridgeFor function is as follows:

According to the logic of bridgeFor, we can find that if the bridge of a specific currency has not been manually set, the default bridge is WETH, that is, if the bridge is not set, the default is to convert the handling fee to WETH. The DIGG coin just didn’t set the corresponding bridge through setBridge.
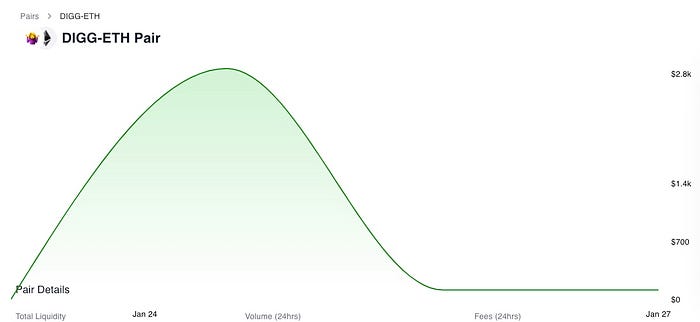
But there is another problem here, that is, during the swap process, if the transaction pair does not exist, the exchange process will fail. In this attack, the DIGG-WETH transaction pair did not exist at the beginning, so the attacker created a DIGG-WETH transaction pair in advance, and then added a small amount of liquidity. If a commission exchange occurs at this time, according to the feature of constant product mentioned above, because DIGG-WETH has very little liquidity, that is, the upper limit of WETH in DIGG-WETH is very small, while the number of commissions to be converted in SushiMaker is relatively small. Larger, such exchange will cause huge slippage. The exchange process will increase the price of WETH to DIGG in the DIGG-WETH trading pair, and all DIGG fee income of DIGG-WETH will be transferred to the DIGG-WETH transaction. By observing the liquidity situation of the DIGG-WETH trading pair, when the liquidity is maximum, there is only less than 2800 US dollars of liquidity. This result can also be mutually verified with the derivation of the formula.
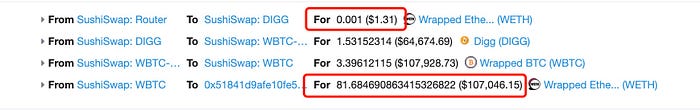
After the attacker completes the fee conversion at SushiMaker, the price of WETH to DIGG in the DIGG-WETH transaction pair has been increased, resulting in a small amount of WETH that can be exchanged for a large amount of DIGG, and the amount of this DIGG is exactly the DIGG-WBTC transaction Most of the fee income.
Sum up
This attack is similar to SushiSwap’s first attack in that they both generate profit by manipulating the exchange price of trading pairs. But the process is different. The first attack was because the attacker used the LP token itself and other tokens to create a new trading pair, and manipulated the initial liquidity to manipulate the price of this new trading pair to make a profit. This attack The use of DIGG itself does not have a WETH trading pair, and the attacker created this trading pair and manipulated the initial transaction price, resulting in a huge slippage during the fee exchange process. The attacker only needs to use a small amount of DIGG and WETH. Huge profits can be obtained by providing initial liquidity.
Related reference links are as follows:
SushiMaker collection fee transaction:
https://etherscan.io/tx/0x90fb0c9976361f537330a5617a404045ffb3fef5972cf67b531386014eeae7a9
Attacker arbitrage trading:
https://etherscan.io/tx/0x0af5a6d2d8b49f68dcfd4599a0e767450e76e08a5aeba9b3d534a604d308e60b
DIGG-WETH liquidity details:
https://www.sushiswap.fi/pair/0xf41e354eb138b328d56957b36b7f814826708724
Detailed explanation of Sushi’s first attack:
https://mp.weixin.qq.com/s/-Vp9bPSqxE0yw2hk_yogFw
About us
SlowMist Technology is a company focused on blockchain ecological security. It was founded in January 2018 and is headquartered in Xiamen. It was founded by a team with more than ten years of front-line network security attack-defense experiences, and the team members have created the security project with world-class influence. SlowMist Technology is already a top international blockchain security company, served many global well-known projects mainly through “the security solution that integrated the threat discovery and threat defense while tailored to local conditions,” including: cryptocurrency exchanges (such as Huobi, OKEx, Binance, etc.), cryptocurrency wallets (such as imToken, RenrenBit, MYKEY, etc.), smart contracts (such as TrueUSD, HUSD, OKUSD, etc.), DeFi projects (such as : JUST, BlackHoleSwap, DeFiBox, etc.), the underlying public chain (such as EOS, OKChain, PlatON, etc.), there are nearly a thousand commercial customers, customers distributed in more than a dozen major countries and regions.
